Fintech APIs: How Financial Services Connect, Authenticate, and Fail
Financial products depend on a fintech API to connect systems, verify users, and complete transactions as one continuous flow. A single action in the interface can trigger several requests across banks, payment providers, and identity services, and each response shapes what happens next. Open finance already supports more than 132 million active users and processes over 330 billion API-driven transactions each year, which shows how central fintech APIs have become to financial services. At this scale, consistency and clarity in how systems respond matter for every product decision.
In this article, our Arounda team explains how these connections work in real products and what helps teams build stable, predictable financial flows.
Article Key Takeaways
In this piece, our Arounda team covers:
- How do financial APIs work in real conditions, and what defines their behavior after go-live
- Core API patterns behind authentication, retries, and transaction states that define stability
- Expert insights on why integrations fail in production, including sandbox gaps and inconsistent flows
- What ISO 20022 migration changes for teams integrating financial APIs in data structure and validation
- Key differences between PSD2 and FDX and how they affect access and consent flows
- Real examples that reveal patterns behind stable API design and integration logic
- Professional tips on structuring flows and reducing integration risks before launch
- A practical checklist to validate integrations and keep systems stable under real usage
Fintech APIs Are a Risk Surface First
APIs in financial services give speed, flexibility, and access to financial infrastructure. However, teams still need to treat them as a risk surface first, since every connection extends system boundaries and exposes core flows to external behavior.
This pattern shows up in real data: 88.7% of financial services firms reported an API-related security incident in the past year, which points to how deeply fintech API integration affects stability and security:
Key points that define this risk surface:
- Each request depends on systems outside your control
- Data moves across services with different validation rules
- Security checks and compliance layers interrupt flows
- Failures propagate across connected systems
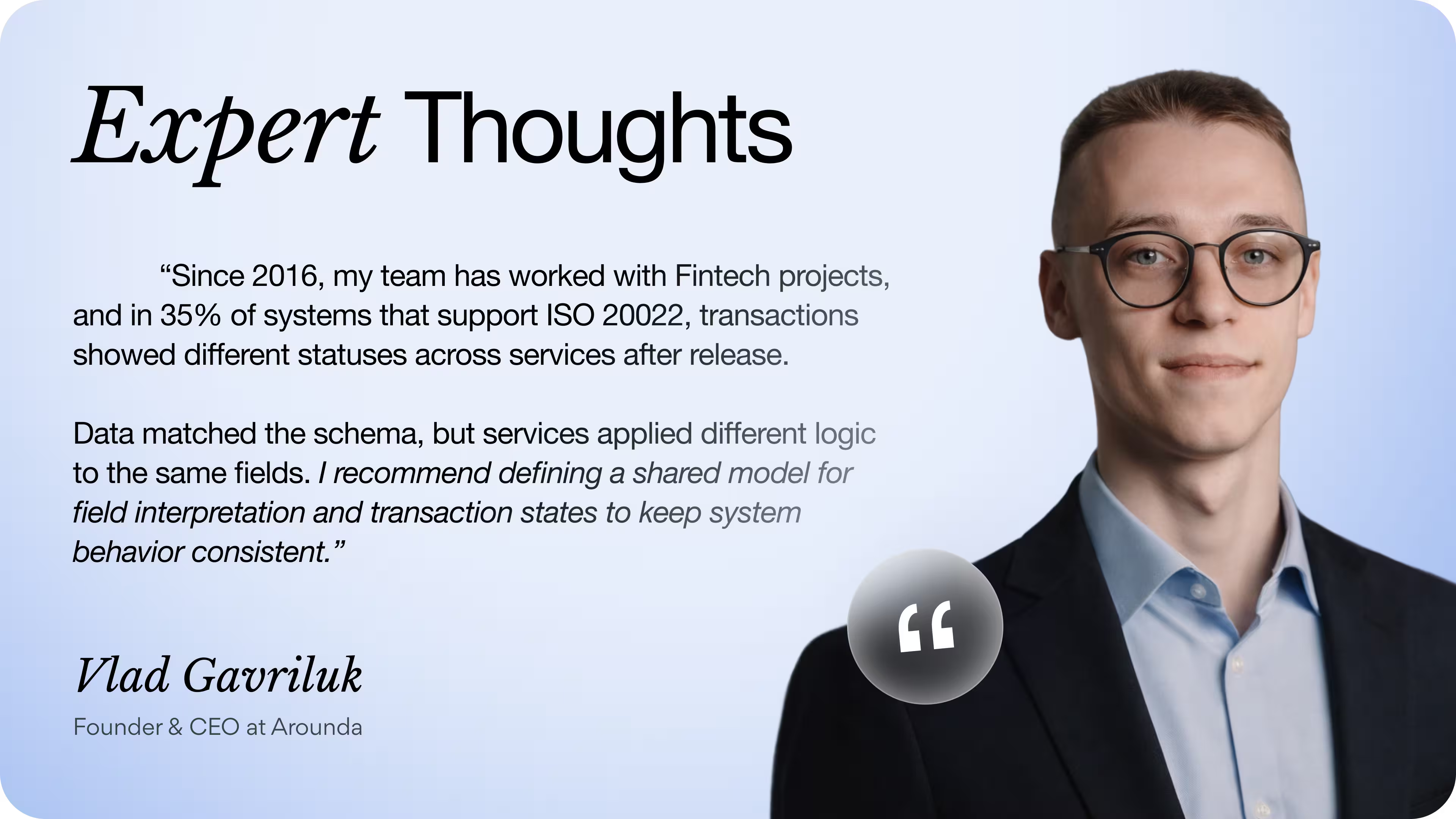
“API integration sets the limits of system reliability long before scale. Each external call introduces behavior you do not control, so teams need strict ownership over validation, monitoring, and fallback states. Stability comes from reducing uncertainty at every step where systems connect.”
Vlad Gavriluk, Founder & CEO at Arounda
Why Financial APIs Fail Uniquely
Financial APIs fail differently since each request passes through several independent systems that respond at different times and under different rules. These layers create the reasons financial APIs behave differently in testing versus live environments, where predictable test flows do not match real transactions. Issues rarely appear as clear errors, which makes failures harder to detect and explain.
Silent failures: your side succeeds, bank's doesn't
Fintech APIs can return a success response on your side while the bank continues processing the request or rejects it later. The interface confirms the action, but the actual transaction stays unresolved, which creates a mismatch between what users see and what really happens.
This usually appears when:
- Requests move through asynchronous processing and return early responses
- Validation rules differ between systems and trigger late rejections
- The final transaction status arrives after the product has already shown success
How to handle this?
Treat early responses as a temporary status and avoid showing a final result until the bank confirms the outcome. The interface should clearly indicate that the operation is still in progress and update the status once the final response arrives. UX/UI audit helps identify where the product shows success too early and correct this logic across real user flows.
Regulatory timeouts disguised as network errors
Regulatory checks can delay a request long enough to trigger a timeout, which the system reports as a network error. This issue appears frequently across API in finance, where fraud screening or identity verification continues after the timeout while the user sees a failure. The mismatch breaks the flow and often leads to repeated actions or abandoned transactions, which directly affects customer experience.
This issue appears when:
- Verification steps run outside the main request timing
- External systems return responses with unpredictable delays
- Error messages do not reflect the actual state of the process
How to handle this?
Move these operations into async flows instead of relying on strict timeouts. Track request state on the backend, allow the process to complete independently, and sync the final result back to the interface. Guide the user through waiting states, limit repeated actions, and show the confirmed outcome without forcing retries.
Authentication Is a Product Decision
Authentication sets the rules for access, session timing, and request validation across connected systems. Every API in fintech depends on these decisions to keep transactions consistent as they move between services. When teams treat authentication as a backend detail, issues appear in real flows where users expect clear and stable outcomes.
Why mTLS gets chosen too late
mTLS secures communication by verifying both sides of a connection, yet many integrations add it only after the first version of a fintech API already works. Teams focus on getting the connection running, while partner requirements and certificate handling stay unclear at the start. This leaves any API for fintech without a consistent trust layer, even though secure connections should be part of the core system logic defined during web development.
This creates problems once real traffic comes in:
- Certificate checks fail and interrupt active requests
- Partner systems reject calls that do not meet security rules
- Authentication changes affect multiple parts of the integration
Arounda team recommends: define authentication requirements with partners before development starts. Set up certificate lifecycle management early, including secure storage and rotation. Test connections under production-like conditions to validate how the system behaves with real security constraints.
Token expiry during a live payment
Token expiry interrupts a payment when the session becomes invalid before the transaction reaches final confirmation. The flow starts with a valid token, yet expires while the user still completes the action, which leaves the system without a clear outcome. This creates a set of token expiry edge cases that break live payment flows in financial APIs:
- The token expires between payment steps and blocks final confirmation
- The system requests re-authentication after the user already initiated the payment
- The session resets and forces the user to restart the flow
These scenarios affect the way product handles continuity and recovery, which often leads to product redesign at the flow level to support consistent transitions between steps.
Arounda recommends: Align token lifetime with real user behavior instead of fixed assumptions. Add session refresh logic that keeps the flow active during critical actions. Design recovery states that allow users to continue the transaction without starting over, and make every step reflect the actual system state.
The Integration Gap Nobody Documents
Most fintech APIs look predictable in documentation, but real behavior often differs once integrations run in production. This gap appears during fintech API integration, where systems apply hidden rules, timing differences, and undocumented constraints. These mismatches shape how APIs behave across environments and lead to issues that teams only discover after launch.
What banking partners document vs. enforce
Banking partners describe how requests should work, yet production systems apply their own rules when they process real traffic. A financial services API can follow the documented format and still return a different outcome once internal checks come into play. This difference explains what banking partners don't document about their API behavior in production, where real decisions depend on account state, transaction context, and risk logic.
What you see in documentation:
- Request structure and expected responses
- Basic validation rules
- Standard error messages
What actually happens in production:
- Dynamic checks based on account, risk, or transaction context
- Stricter validation under real transaction conditions
- Limits and rules that appear only under load or sensitive actions
Arounda team recommends: Capture how partners actually respond under different conditions and turn those responses into clear product states. Define what the user sees when a request gets rejected, delayed, or flagged for additional checks, and keep these states consistent across flows. This level of mapping often takes shape during web design consulting, where product teams align interface logic with how partner APIs behave in production.
Sandbox behavior that betrays production reality
Sandbox environments simulate API behavior, but they remove many real conditions. This creates a gap where an API in fintech works as expected in testing, yet behaves differently once real users, data, and verification flows come into play.
What sandbox does not reflect:
- Real authentication flows with expiring sessions and retries
- Timing shifts caused by external checks and system load
- User actions that change the order and pace of requests
- Full validation logic applied to real transactions
This is where teams start seeing fintech API authentication failures that happen only in production not sandbox, since authentication paths behave differently under real conditions.
To avoid these issues, teams need to define real scenarios early and test flows beyond ideal cases. Work at the product discovery stage helps surface these conditions in advance, so product decisions account for real user behavior, delays, and edge cases before the system reaches production.
A good example of how real usage differs from expected scenarios is the work we did with PayPossible, a fintech platform that connects merchants, lenders, and banks. The client came with complex flows and unclear product logic that did not match how users actually interacted with the system. We redesigned the platform structure, simplified onboarding, and aligned flows with real user behavior, so users could understand the product and complete actions without confusion.
As a result, merchant signups doubled, completed financing applications grew by 40%, and user satisfaction reached 88%. This redesign also received a UI award on Behance, highlighting the strength of its visual design and overall usability.
Version drift between release cycles
Version drift appears when connected systems update on different schedules and stop behaving in sync. A fintech API integration can rely on one version during development, while another service already runs updated logic in production. This creates small differences that grow over time and affect how requests and responses work across the system.
You start to notice it when:
- Response formats change and break parsing logic
- New fields appear or existing ones change meaning
- Validation rules shift between releases
- One service updates earlier and disrupts dependent flows
Arounda recommends: Track API versions across all integrations and plan updates as coordinated changes. Define versioning rules, monitor partner updates, and test compatibility before each release. Validate changes in real user flows and confirm that each update keeps the integration stable across scenarios.
API Categories Ranked by Integration Complexity
Financial systems rely on different types of APIs, and each category requires a different level of effort to connect and maintain. The complexity of a fintech API grows as it moves closer to money movement, user identity, and core system logic. From Arounda experience, we grouped fintech API categories ranked by how difficult they are to integrate, starting from the simplest and moving toward the most complex.
Open Banking APIs
Open Banking APIs give access to a user's financial data, such as balances and transaction history. Products use them to connect accounts and display insights without changing anything in the underlying system. This makes them the easiest to work with, since requests stay predictable and do not affect the financial state.
Payment APIs
Payment APIs handle purchases, transfers, and payouts between accounts. A typical setup connects your product to a payment provider and manages the flow from initiation to final confirmation. The level of difficulty increases here, as every action must stay accurate and the system needs to deal with retries, failures, and partial transaction states.
Identity & KYC APIs
Identity and KYC (Know Your Customer) APIs control access and verify users before they can perform financial actions. These flows rely on tokens, session handling, and external verification services, which adds dependency on multiple systems. The integration becomes more demanding due to strict security requirements and situations where sessions expire, or checks interrupt the flow.
Lending & Financial Product APIs
These APIs power product logic such as loan approvals, limits, and user-specific financial conditions. Each response depends on business rules, risk evaluation, and user data, which ties backend logic closely to user flows. This category brings higher complexity, and teams often rely on financial services design to keep these interactions structured and understandable across finance APIs.
Banking Infrastructure APIs
Banking infrastructure APIs connect directly to core systems like accounts, ledgers, and internal transaction processing. They operate across multiple services that must stay synchronized while handling real financial operations. This is the most complex category, since even small inconsistencies can affect the entire system, and teams often use bank web design to translate this complexity into stable and usable product flows.
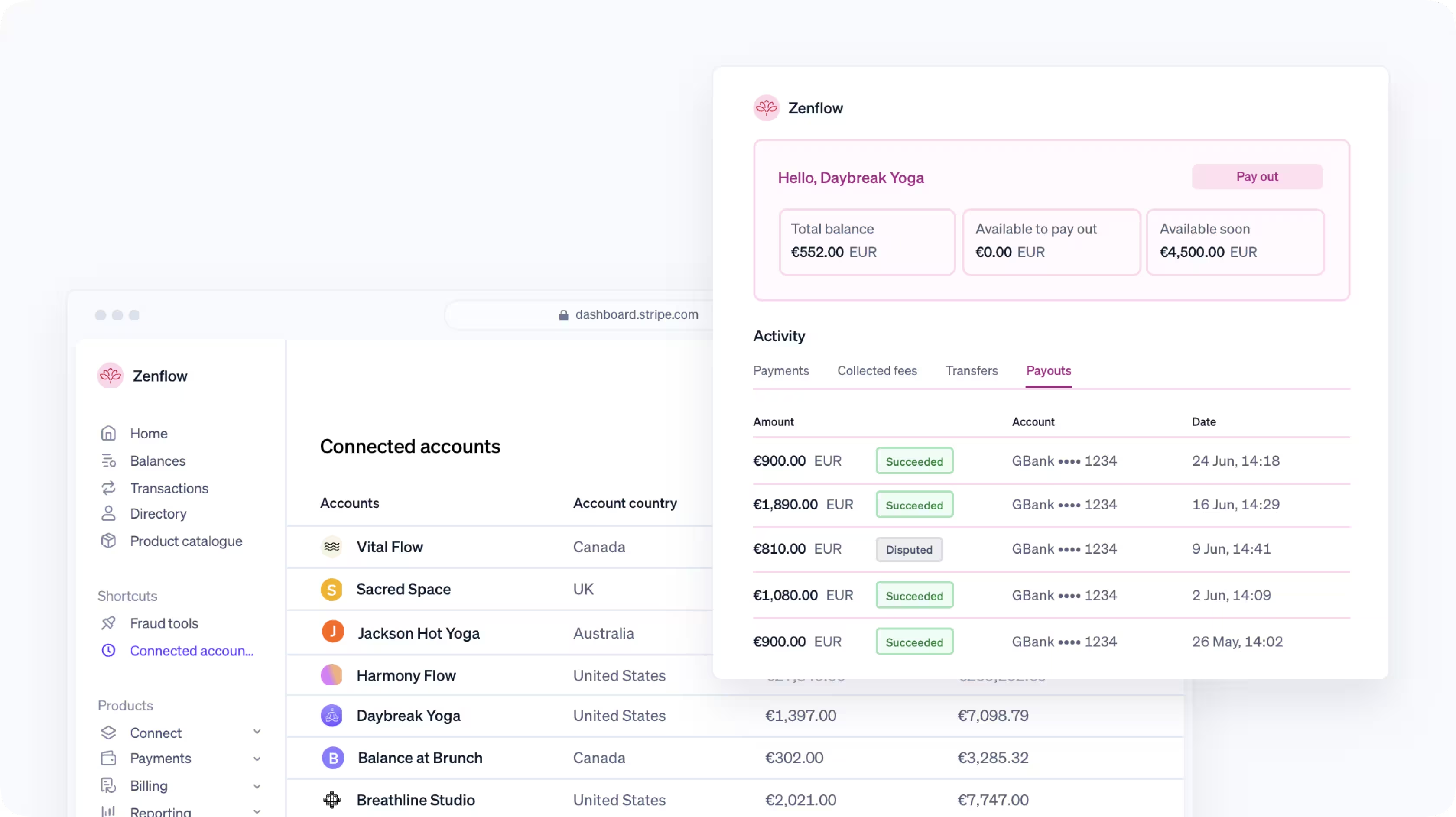
A good example of working with complex financial systems is the project we delivered for FlowFunds, a fintech platform that combines personal finance management, digital banking, and investment tools into one product. The client needed to unify multiple financial functions and bring clarity across platforms where the experience felt fragmented.
Our team created a consistent design system, restructured dashboards, and aligned key flows such as transfers, account management, and navigation across web and mobile. This helped translate complex backend logic into clear user actions and made core operations easier to understand and complete.
The results were 2× user growth within six months, over 150k+ new users per month, a 40% increase in session time, and 90% user satisfaction.
What ISO 20022 Changes at API Level
ISO 20022 sets a unified standard for financial data exchange and replaces fragmented formats with structured, detailed messages. It defines required data fields for each transaction and sets clear rules for interpretation across the full fintech API integration.
At the API level, this changes how systems operate in practice:
- Requests include structured fields that must match strict schemas
- Responses return detailed transaction states instead of simple success or failure
- Payloads carry more context, which affects processing across services
- Systems follow shared financial API standards, which limit custom formats
These changes turn APIs into structured messaging layers where every field carries meaning and must stay consistent across systems.
Idempotency and the Duplicate Transaction Problem
Idempotency ensures that one action leads to one result, even if the same request repeats. This is what idempotency actually means for payment API integration, where systems must recognize repeated requests and return the original outcome instead of creating a new transaction. The duplicate transaction problem appears when this control is missing, and the same payment gets processed more than once.
Typical fintech API integration mistakes that create duplicate transactions in banking systems are:
- Missing idempotency keys for repeated requests
- No storage of previous transaction results
- Delayed or unclear transaction status
- Repeated user actions triggered by weak feedback in UI/UX Design
How to prevent duplicate transactions?
Assign a unique idempotency key to each transaction and store the result before confirmation. Return the same response for repeated requests instead of creating a new operation. This keeps payments consistent even when retries, delays, or repeated actions occur.
A relevant example here is our work with Klasha, a fintech company that delivers cross-border payment solutions for businesses and individuals. The client needed to simplify complex payment flows and make borderless transactions feel clear and manageable for everyday users.
Our design team built a unified brand and UI/UX system, created high-fidelity wireframes to clarify structure and logic, and designed the transaction flow and mobile banking experience around intuitive, user-friendly steps. This helped users move through payment actions with less friction and gave the product a clearer operational structure.
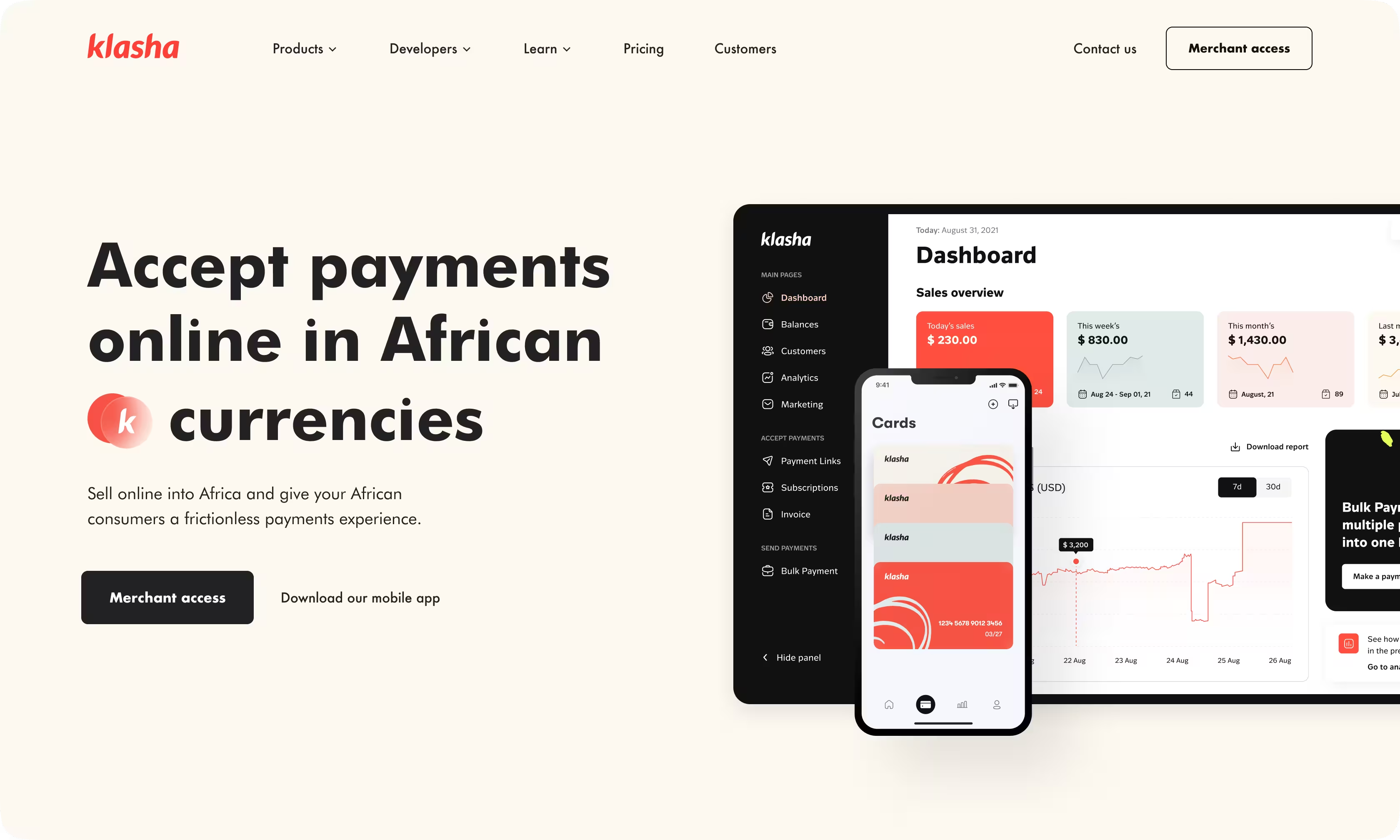
As a result, the project achieved a 30% increase in conversion rates, a 35% improvement in user satisfaction, reached 180K+ active users, and surpassed 300K+ app downloads.
Open Banking APIs Across Regulatory Regimes
Open banking APIs vary across regions, since each market sets its own rules for access, security, and data exchange. These differences directly shape how fintech APIs operate in real products and define the constraints teams face during integration.
PSD2: what compliance changes in API design
PSD2 (Revised Payment Services Directive) is a European regulation that requires banks to provide secure API access to accounts and payments for third-party services. It enforces strict rules around user consent, data access, and strong customer authentication, which every product must follow to operate in this ecosystem.
In practice, this directly shapes fintech API integration and forces teams to design APIs and flows around compliance requirements:
- Add strong customer authentication steps for payments and sensitive actions
- Manage user consent explicitly and track it across sessions
- Handle multiple transaction states such as pending, authorized, or rejected
- Design APIs that support secure redirects between the bank and the product
- Align request and response structures with regulated formats
These requirements make API design more controlled and consistent, but they also add complexity to system logic and product flows that teams need to account for from the start. It becomes especially visible in enterprise website design, where multiple systems and states need to stay aligned.
FDX: permissioned data without unified mandate
FDX (Financial Data Exchange) is an industry standard in the United States that defines how financial institutions share data through APIs with user permission. It sets a common structure for requests, responses, and consent handling, so users can grant and manage access to their financial data without relying on credentials like passwords.
In real integrations, FDX shapes how the API for fintech handles access and data exchange:
- User consent becomes a required step before any data request
- APIs return structured financial data based on agreed schemas
- Access tokens replace direct credentials and control session scope
- Integrations rely on consistent patterns, but each provider configures them within its own system
This approach gives teams a clear foundation for building secure data access, while still requiring careful handling of consent, sessions, and data structure across different implementations.
Where regulatory gaps create integration problems
Different regulatory approaches create gaps between systems that need to work together. The open banking API differences between PSD2 in Europe and FDX in the United States lead to mismatched rules for authentication, consent, and data exchange, which makes integrations harder to align in real products.
This usually shows up as:
- The same action requires different authentication steps in different regions
- Consent flows break or reset when systems follow different rules
- Data arrives in similar but incompatible structures
- One integration works in one market but fails in another without clear errors
How to handle regulatory differences?
Build your integration around a single internal flow and treat external APIs as inputs to adapt. Normalize authentication, consent, and data before they reach your core logic, so the product behaves the same way even when underlying regulations differ.
Fintech API Examples Worth Studying
Here are some of the best fintech API examples that show what effective API design looks like in real financial products and why these approaches work.
Stripe: what their API structure reveals
Stripe stands as one of the most reliable fintech API platforms for payments, and its structure reflects a clear, system-driven approach to financial operations. It models core entities like customers, payments, and charges as separate resources, which keeps backend logic aligned with real transaction flows.
Key takeaways from their API structure:
- Each payment goes through defined states, so the system always knows what happens with a transaction
- Idempotency keys allow the same request to repeat safely without creating duplicate charges
- Resources match real actions, like creating a customer or confirming a payment
- Responses return predictable fields and statuses, so teams can handle success and failure without guesswork
This example shows that Stripe reduces payment risk through structure. A request becomes a tracked operation with clear states, consistent responses, and safe retries. Teams that apply this model gain visibility into each step and keep behavior stable when networks delay or users repeat actions.
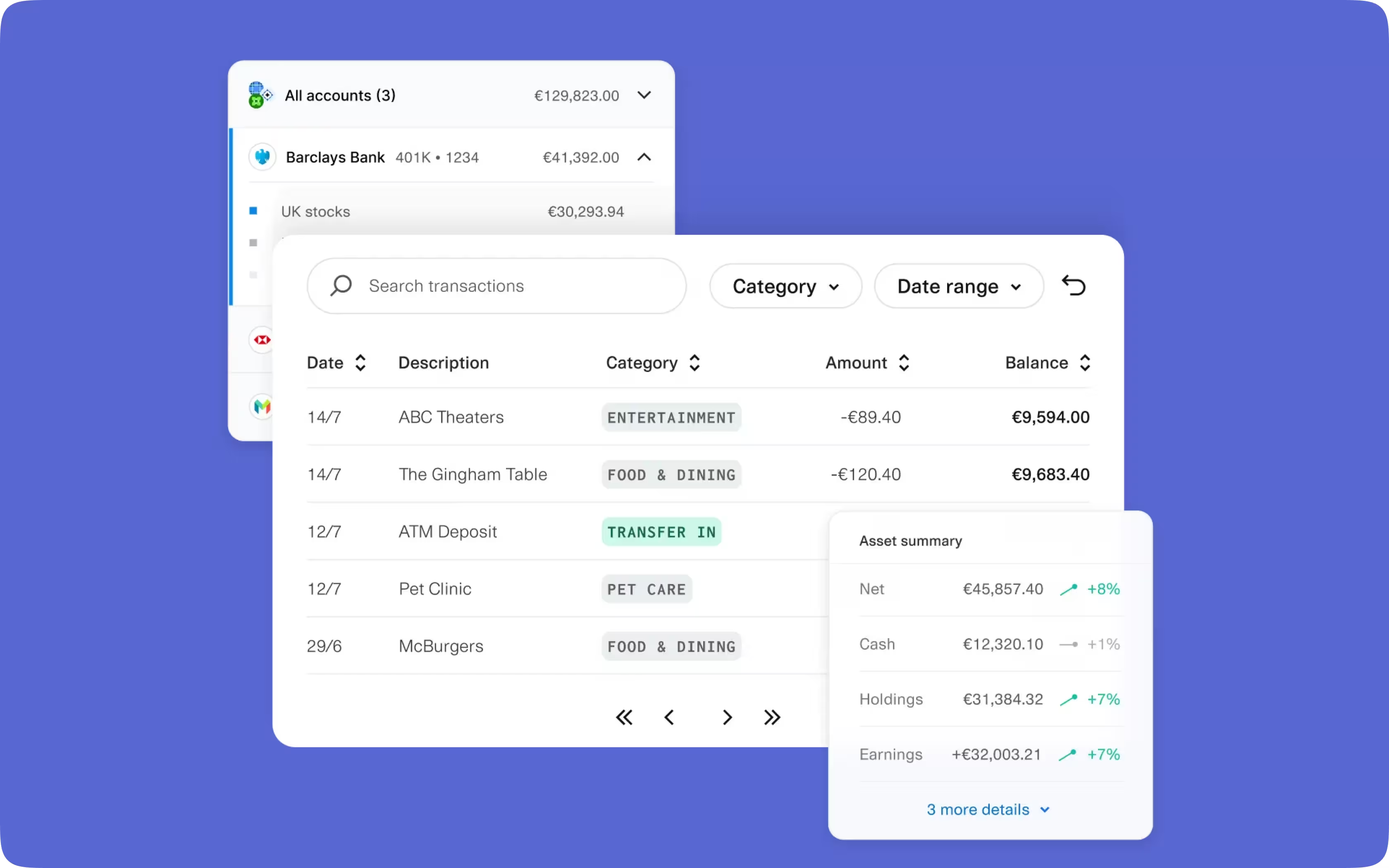
Plaid: aggregation under regulatory pressure
Plaid connects apps to users’ bank accounts and pulls financial data from multiple institutions into one place through a single API for fintech. It lets products show balances, transactions, and account details without building separate integrations for each bank, while access depends on user consent and the rules each provider enforces.
What makes this approach effective:
- Combines data from many banks into one unified interface
- Standardizes account and transaction data despite differences between providers
- Uses consent-based access with tokens instead of direct credentials
- Supports multiple connection methods, depending on what each bank allows
- Maintains stable data delivery even when access rules or data availability change
This example shows why aggregation becomes a system-level problem as soon as multiple providers are involved. Teams need to control how data enters the product, align it to one structure, and account for changes on the provider side, since these factors directly affect stability and product behavior over time.
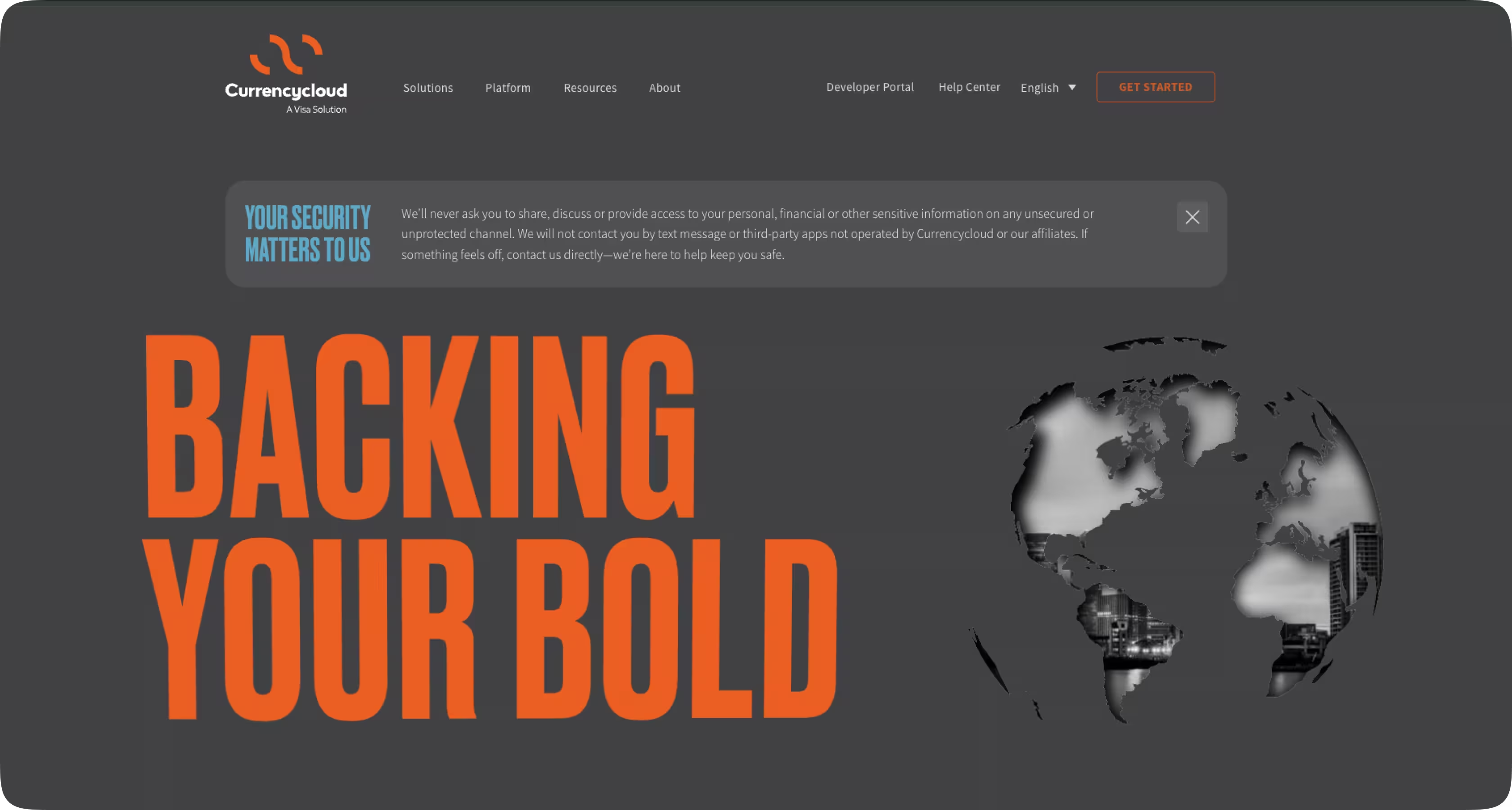
Currencycloud: what most teams build manually
Currencycloud handles cross-border payments, currency exchange, and multi-currency accounts through a single fintech API. It packages the operational layer behind international money movement into one system, which many teams try to assemble piece by piece when building similar products.
What makes it a good reference:
- Exposes complex FX and payment operations as clear, structured endpoints
- Keeps balances, transfers, and conversions within one consistent system
- Handles routing and compliance inside the API instead of pushing it to the client side
- Returns predictable transaction states, which keep flows traceable and controlled
- Unifies fees, rates, and transaction data so teams work with a single source of truth
This example shows that strong fintech APIs reduce system fragmentation and centralize critical logic. Teams that rely on this approach gain better control over financial flows and avoid rebuilding complex infrastructure across multiple layers.
Pre-Launch Fintech API Integration Checklist
Final Thoughts
API in fintech shapes how systems behave once real users, data, and transactions enter the flow. Issues appear when operations lack clear states, retries create uncertainty, or when differences between providers and regulations break consistency across environments. We covered how stable integrations rely on structured flows, controlled transaction handling, and predictable data across systems. When these elements stay aligned, products handle real conditions without unexpected failures.
Arounda works with fintech products to structure API-driven systems, align logic with real usage, and keep integrations stable as products grow. If you want to build or improve a fintech product that performs reliably in production, contact us.

Table of contents
FAQ
Standard REST APIs handle simple data exchange through request–response cycles. Fintech APIs operate with financial transactions, where each request must stay accurate and traceable. They add strict authentication, consent handling, and state tracking, along with controlled retries to prevent duplicate actions.
Financial APIs show their real behavior only after launch, when they connect to live providers and handle real transactions. Differences between sandbox and production, unstable external systems, and edge cases start to surface. If the system does not handle retries, timeouts, and inconsistent responses from the start, these issues break flows and lead to failures.
PSD2 requires teams to implement strong customer authentication, manage user consent, and connect to bank APIs through secure flows. Each request must respect access scopes and session rules, and the system must track consent and authentication status at every step. This adds extra steps to payment and data access flows and requires strict control over how requests move between systems.
Sandbox environments simulate API behavior, but they do not reflect real provider systems, data variability, or edge cases. Production introduces differences in response timing, data formats, and failure scenarios that sandboxes often skip. These gaps lead to unexpected errors and broken flows if the integration relies only on test environment results.
Financial operations must stay exact, even when requests repeat due to timeouts or network issues. Idempotency ensures the system processes the same request once and returns the same result on retry. Without it, repeated requests can create duplicate transactions, which leads to incorrect balances and financial errors.
Teams need to consider standards that define data, access, and compliance before integration starts. ISO 20022 sets the structure of financial data and messages. PSD2 and FDX define rules for authentication, consent, and access to financial data. These standards shape how APIs behave and what systems must support during integration.

89+ Reviews
on Clutch

Top Rated Plus Agency
on Upwork

Top 50 Trending team
on Dribbble

Projects are Featured on Behance platform